LDAP
From HP-SEE Wiki
The authentication and authorization of supercomputer users is significantly different from similar solutions applied in grids. While the former often requires local personalized user credentials as well as local user access to at least the HPC font-end nodes, the later uses temporary local credentials assigned to individual user jobs rather than to individual users. Furthermore in the grid case the users are authenticated and authorized by the grid middleware (i.e. in the application level), rather than the lower, say operating system level, software layers.
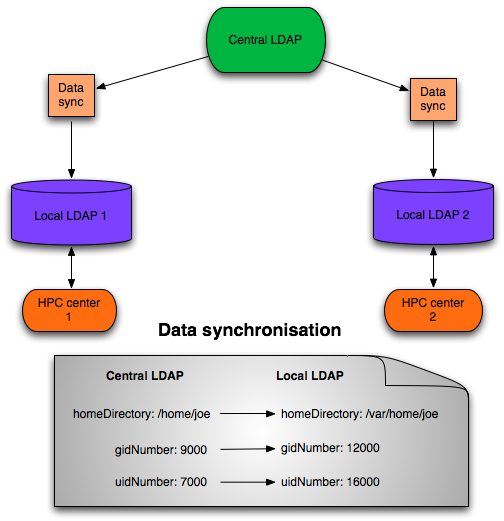
When creating a structured HPC network an appropriate convergence between the two are needed combining the advantages of both. The classic way of having OS-level user credentials on HPC facilities is to use centralized, yet fail-safe LDAP databases to store user and group parameters and expose them on all HPC elements: compute, front-end and storage elements uniformly. Even though it works quite well in any local configuration, in the everyday practice it is difficult to share multiple LDAP servers administered over multiple organizations. One fallback strategy might be to build up a directory service, a hierarchically built LDAP database that has multiple subtrees and each subtree belongs to different organizations.
Figure shows the LDAP topology of HP-SEE. There is a central LDAP, which content each HPC center and user. The HPC centers also have local LDAP server. The data synchronization between the central LDAP and local LDAP is done by a script. This script do the mapping, it is essential for example if the uidNumber need to be changed. The users are authenticated from this local LDAP service. It is important that the userid need to be extended with a “see-“ prefix because they need to be unique in each HPC center’s LDAP.
Central LDAP server installed on this machine: see-ldap.grid.niif.hu. It can be accessed over LDAPS. The server’s certificate issued by TERENA CA.
Here is a LDAP Data Interchange Format (LDIF) example for a user in the central LDAP:
dn: uid=see-john,ou=users,dc=hp-see,dc=eu objectClass: organizationalPerson objectClass: inetOrgPerson objectClass: account objectClass: X509DistinguishedName cn: John gecos: John Brown,,, gidNumber: 15000 homeDirectory: /home/see-john loginShell: /bin/bash mail: john@brown.hu sn: Brown uid: see-john uidNumber: 15000 X509DN: "/C=HU/O=NIIF CA/OU=GRID/OU=NIIF/CN=John Brown"
Authorization to a HPC center:
dn: cn=fep.grid.pub.ro,ou=hpc-groups,o=romania,dc=hp-see,dc=eu objectClass: groupOfUniqueNames cn: fep.grid.pub.ro uniqueMember: uid=see-martin,ou=users,dc=hp-see,dc=eu uniqueMember: uid=see-joe,ou=users,dc=hp-see,dc=eu
If we would like to authorize an user then we need to add the user’s DN to the required HPC center’s tree.
The see-ldap.grid.niif.hu machine is protected with firewall so if a HPC site would like to access it then the site’s admin need to send a mail to Gabor Roczei (NIIFI)